Today is D-Day for banks and the City of Johannesburg to pay ransom demands sent through by hackers last week. Bryan Hamman, Regional Director at NETSCOUT, which offers NETSCOUT Arbor, specialising in advanced DDos protection solutions, offers this explanation of DDoS attacks in the broader cyber security landscape.
Cyberattacks have been around since the dawn of the internet. What initially started off as curiosity or bragging rights, quickly escalated to monetising the activity. In a world where every piece of personal data is of value, the more you have, the more you can bank.
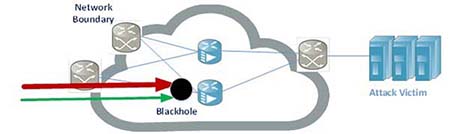
Historically, internet service providers would merely ‘blackhole’ any attack traffic. This rudimentary tactic would drop the attack traffic but also any valid traffic towards the intended target. In many cases this would merely achieve what the attacker wanted, which was to take the target offline.
In around 2000, a team of students from the University of Michigan began working on a better way to tackle the problem. In the coming years, the company they formed, namely Arbor Networks, pioneered the fight against cyberattacks and quickly became the leading provider of attack mitigation for service providers globally.
The idea, although simple in principle, was far more challenging in execution as attackers constantly evolved as well. The goal of the solution was to clean all attack traffic without any impact to the valid traffic to one or more victims of cyberattacks. Using a non-inline device, Arbor pioneered the local scrubbing of malicious traffic within service provider environments.
 This became a game changer and today Arbor (now a part of NETSCOUT) actively works with, and is the vendor of choice for, over 90 percent of the top Tier 1 and Tier 2 ISPs in the world.
This became a game changer and today Arbor (now a part of NETSCOUT) actively works with, and is the vendor of choice for, over 90 percent of the top Tier 1 and Tier 2 ISPs in the world.
Later in 2007, a collaborative effort began between Arbor and its ISP customers to share data on the type of malicious traffic seen across the globe. The idea was to reverse- engineer, curate and create unique ‘fingerprints’ of the bad traffic and share it with other providers, so that as a group they could more easily identify and block this traffic at the edge of their respective networks.
Today, ATLAS boasts over 380 ISPs who are sharing data. This unique collaboration is translated into the intelligence feed that Arbor sends back into its products as the real-world visibility of what is happening. NETSCOUT enterprise and ISP customers use the cyber security intelligence feed from Arbor to keep their networks and customers safe. This value proposition is unmatched in the fight against cyber-attacks.

With the rise of the Internet of Things (IOT), the rapid increase in last mile connectivity and the shift to global ecommerce, enterprises have more frequently become the targets of various forms of cyberattacks. The problem, however, is that traditional vendors of firewalls, IPS, WAF and such are ill-equipped to handle these new and emerging threats.
Firstly, they are often the victim of the attack, as state and application-based attacks are frequently used to target security appliances that by design have to track sessions. These devices have a limited amount of memory and CPU, which translates to a fixed number of sessions or packets the device can handle. Attacks can be crafted to expose those weaknesses. A far simpler method would be to just saturate the last mile of connectivity. Regardless of dropping traffic on the customer side, the entire customer site would be affected.
NETSCOUT | Arbor has a globally unique solution in not only blocking both inbound and outbound connections that are deemed to be suspicious, but it also has the ability to work with Arbor-enabled service providers to facilitate automated local ‘cloud’ scrubbing for the enterprise customers, with no changes required to the infrastructure or routing.
This is of major benefit over the use of DNS or BGP methods used with cloud scrubbing, as there is no additional latency not only to the valid traffic to the attack victim, but also as regards all other traffic that would be affected when using BGP due to the /24 minimum block requirement. Enterprise customers can procure the device themselves or, in the majority of cases, as part of a managed service from their upstream ISP.
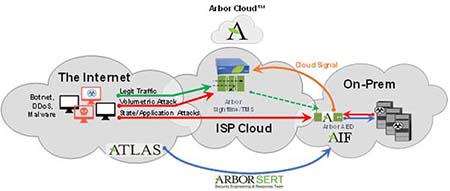
The AED is an inline layer 2 transparent device that by design is stateless in nature. It has the ability to block both inbound attacks and outbound dubious communications. The AED is backup by a near real-time intelligence feed from the ATLAS research team, allowing the device is identify and stop new and emerging threats. Insertion into existing networks requires no changes to the underlying architecture.
Looking at the local footprint we have seen a drastic increase in cyber-attacks, and this is something that local companies have historically not given much consideration to. The publicly-documented cases at Cool Ideas, Cybersmart and various South African public services illustrate that more and more attacks can be expected. The growing level and frequency of attacks are not only limited to local ISP and enterprises, but even global giants have been taken down in recent weeks with successful attacks against Google and AWS.
NETSCOUT | Arbor releases a Cyber Threat Intelligence report every six months based on the work done by ASERT, the Arbor Security Engineering and Research Team. The statistics over the past six months compared to 2018 show a clear and dangerous trend in both the size and frequency of attacks.
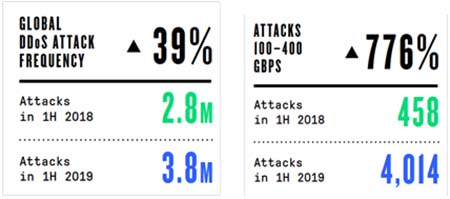
Overall there was increase in attacks in the first six months of 2019, with a slight drop in the maximum size of the attack compared with the first half of 2018.
For a copy of the latest Threat Intelligence Report, or a glimpse into the real time global attack landscape, please visit: https://horizon.netscout.com

Netscout | Arbor is the leading vendor in protecting Service Provider networks while working with Enterprise customers to formulate a hybrid defence in depth solution that provides the highest level of protection with the least amount of disruption to daily functional operations of their business.
 NETSCOUT SYSTEMS, INC (NASDAQ: NTCT) assures digital business services against disruptions in availability, performance, and security. Our market and technology leadership stems from combining our patented smart data technology with smart analytics. We provide real-time, pervasive visibility, and insights customers need to accelerate, and secure their digital transformation.
NETSCOUT SYSTEMS, INC (NASDAQ: NTCT) assures digital business services against disruptions in availability, performance, and security. Our market and technology leadership stems from combining our patented smart data technology with smart analytics. We provide real-time, pervasive visibility, and insights customers need to accelerate, and secure their digital transformation.
